eCommerce servers are becoming specific with remote accessibility malware that hides on Nginx servers in a way that helps make it nearly invisible to stability solutions.
The risk received the name NginRAT, a mixture of the application it targets and the remote obtain capabilities it presents and is being applied in server-aspect attacks to steal payment card details from on the net suppliers.
NginRAT was discovered on eCommerce servers in North The us and Europe that experienced been contaminated with CronRAT, a remote access trojan (RAT) that hides payloads in jobs scheduled to execute on an invalid day of the calendar.
NginRAT has infected servers in the U.S., Germany, and France the place it injects into Nginx procedures that are indistinguishable from genuine ones, permitting it to keep on being undetected.
RATs help server-aspect code modification
Scientists at safety business Sansec explain that the new malware is shipped CronRAT, though both of them satisfy the identical functionality: delivering remote entry to the compromised method.
Willem de Groot, director of risk exploration at Sansec, told BleepingComputer that though utilizing incredibly distinctive techniques to sustain their stealth, the two RATs surface to have the identical job, performing as a backup for preserving remote obtain.
Whoever is behind these strains of malware, is employing them to modify server-side code that permitted them to file facts submitted by people (Article requests).
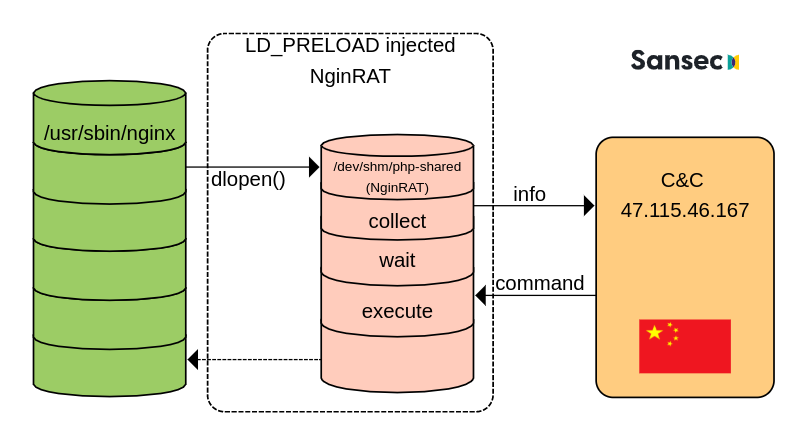
Sansec was capable to analyze NginRAT immediately after making a custom made CronRAT and observing the exchanges with the command and management server (C2) positioned in China.
The researchers tricked the C2 into sending and executing a rogue shared library payload, as portion of the normal malicious conversation, disguising the NginRAT “more advanced piece of malware.”
“NginRAT primarily hijacks a host Nginx software to keep undetected. To do that, NginRAT modifies core features of the Linux host process. When the respectable Nginx world-wide-web server employs such operation (eg dlopen), NginRAT intercepts it to inject itself” – Sansec
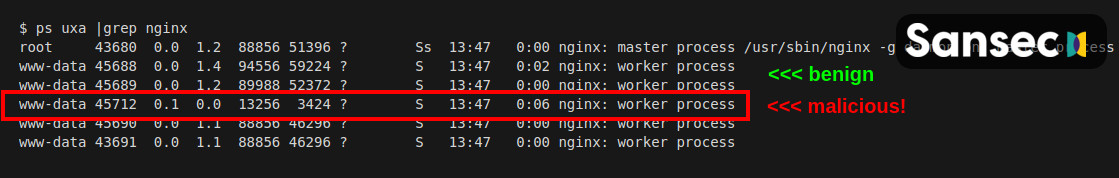
At the conclude of the method, the Nginx process embeds the remote access malware in a way that tends to make it just about unattainable to convey to aside from a legitimate approach.
In a technical report today, Sansec explains that NginRAT lands on a compromised system with the support of CronRAT by using the tailor made “dwn” command that downloads the destructive Linux process library to the “/dev/shm/php-shared” locale.
The library is then launched employing the LD_PRELOAD debugging element in Linux that is typically applied to test procedure libraries.
Possible to mask the execution, the risk actor also added the “help” choice various occasions at the close. Executing the command injects the NginRAT into the host Nginx application.
Simply because NginRAT hides as a ordinary Nginx system and the code exists only in the server’s memory, detecting it could be a obstacle.
Even so, the malware is released applying two variables, LD_PRELOAD and LD_L1BRARY_Path. Directors can use the latter, which has the “typo,” to reveal the lively malicious procedures by working the subsequent command:
$ sudo grep -al LD_L1BRARY_Route /proc/*/environ | grep -v self/
/proc/17199/approximativement
/proc/25074/environSansec notes that if NginRAT is identified on the server, administrators should also test the cron responsibilities simply because it is incredibly probable that malware is hiding there, too, additional by CronRAT.




More Stories
Supply Chain And Logistics Hurdles In Cross-Border E-Commerce
Micro-Influencers Impact On Niche Markets In Social Commerce
Cultural And Language Barriers In Cross-Border E-Commerce Customer Experience